GitHub Actions Secrets
In this blog post I explore the different ways in which you can store secret data within GitHub and how to recall them into a workflow.

GitHub Actions is a tool that can be used to automate processes that relate to code stored within a repository. You can use it to automate your Continuous Integration/Continuous Deployment (CI/CD) processes.
When carrying out this kind of automation you need to be able to store sensitive data somewhere. GitHub Actions Secrets can be used to store that sensitive data.
GitHub allows you to store secrets at 3 different levels:
- Repository
- Environment
- Organization
In this article, we will look at those three levels, and how to call secrets in an example GitHub Actions workflow.
Repository secrets
Repository secrets are tied to the repository they are created within. You can store 100 secrets per repository.
Add a repository secret
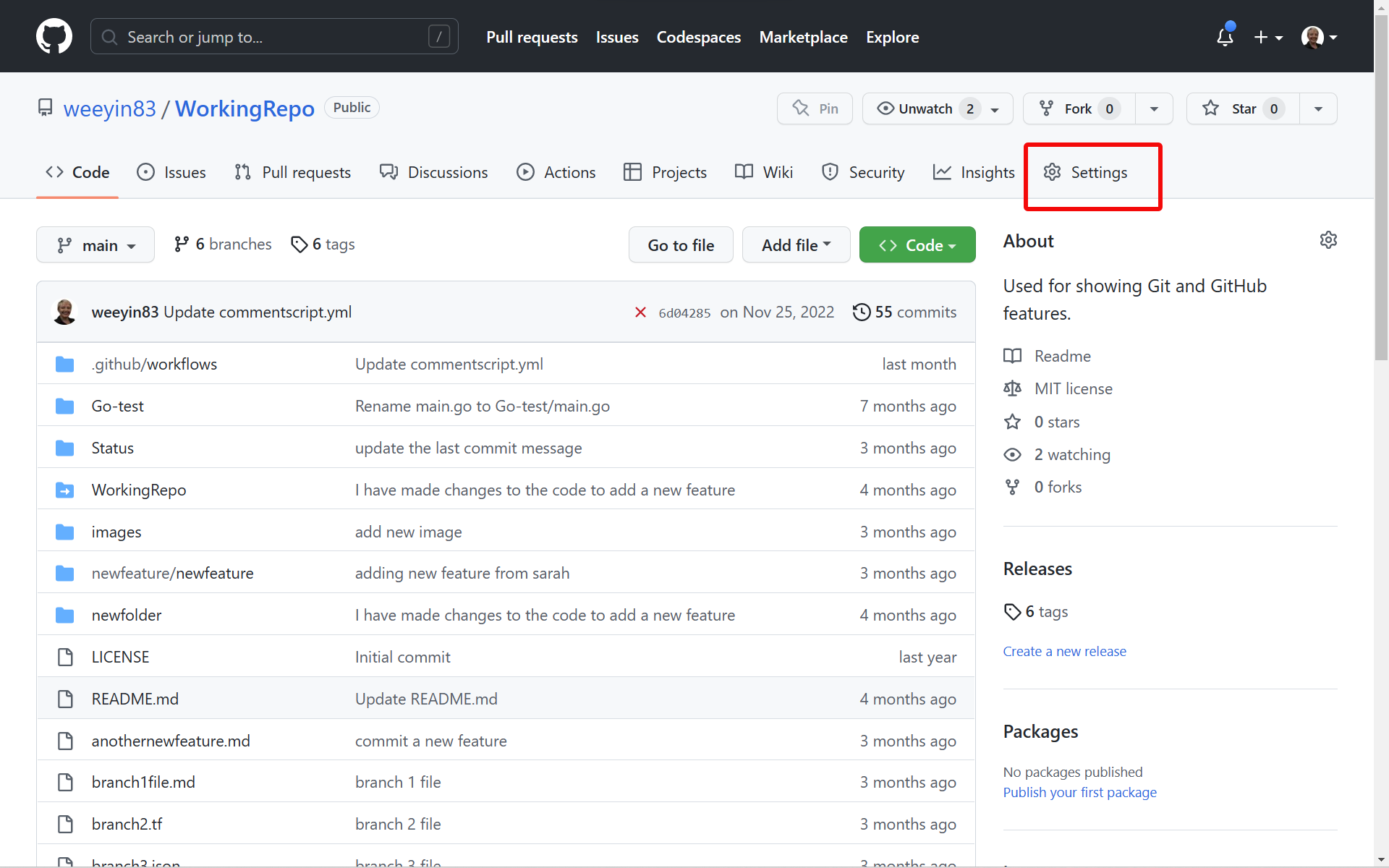
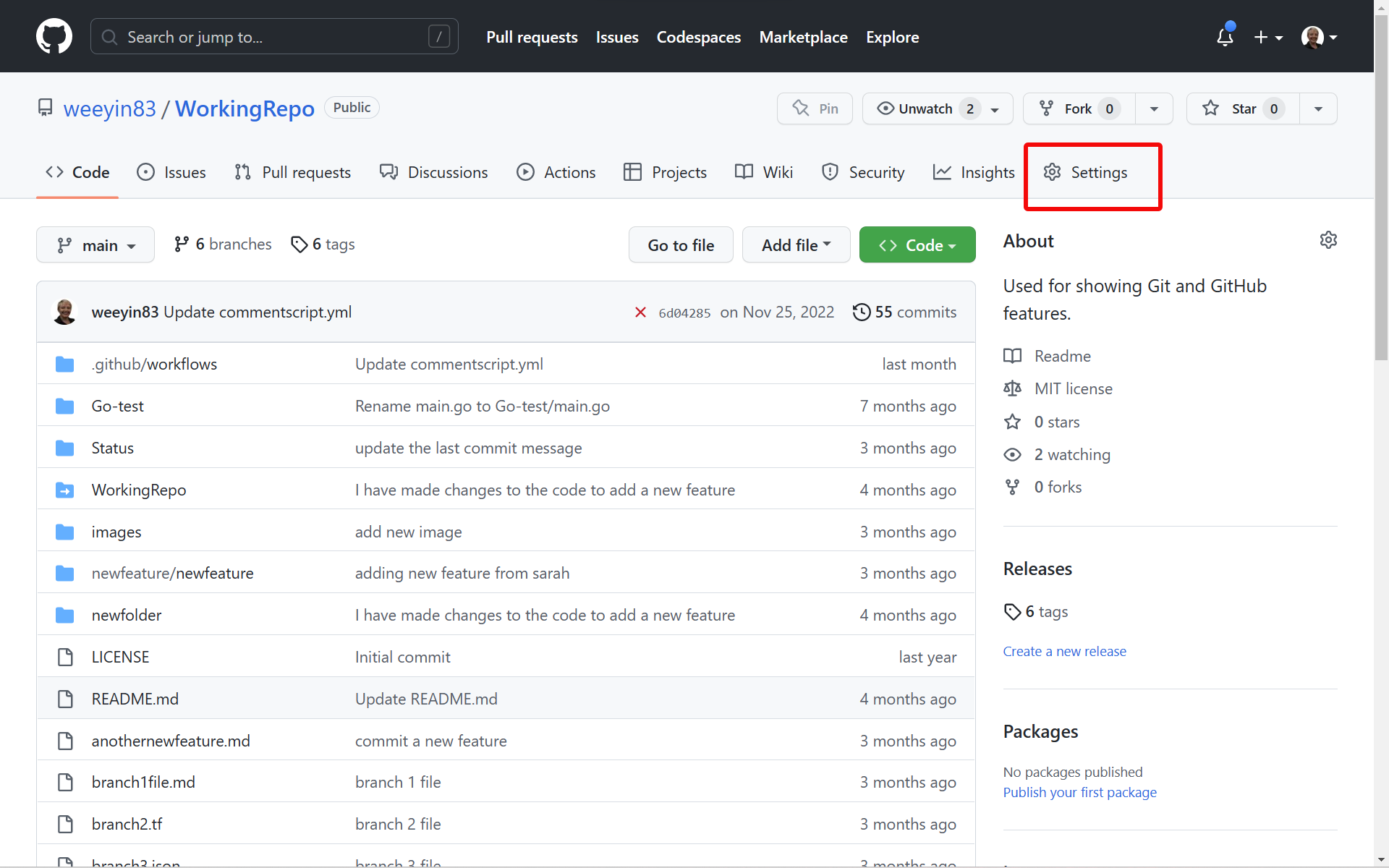
Open your project’s repository and click on Settings in the top menu
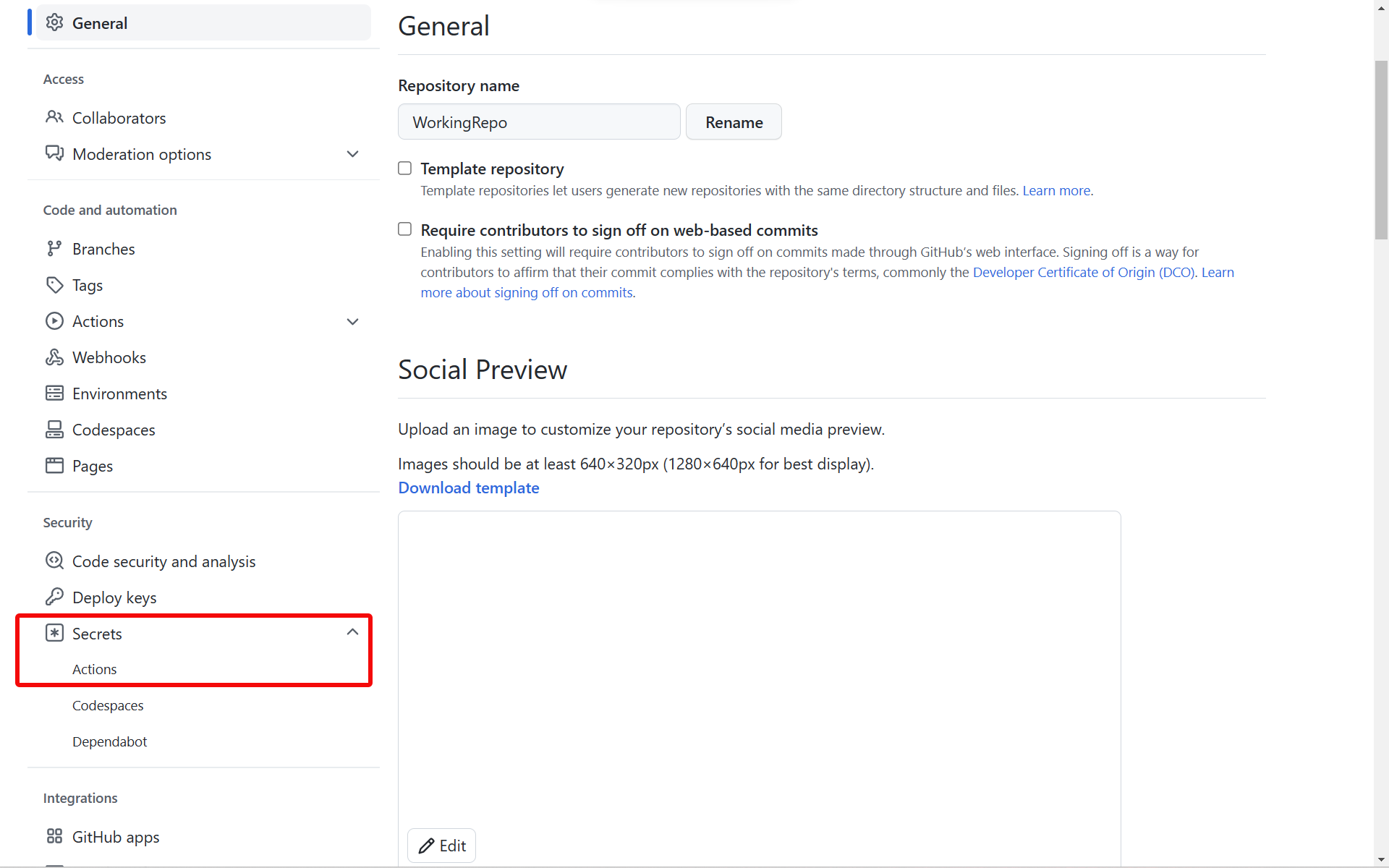
Click Secrets in the menu on the left-hand side.
Then select Actions.
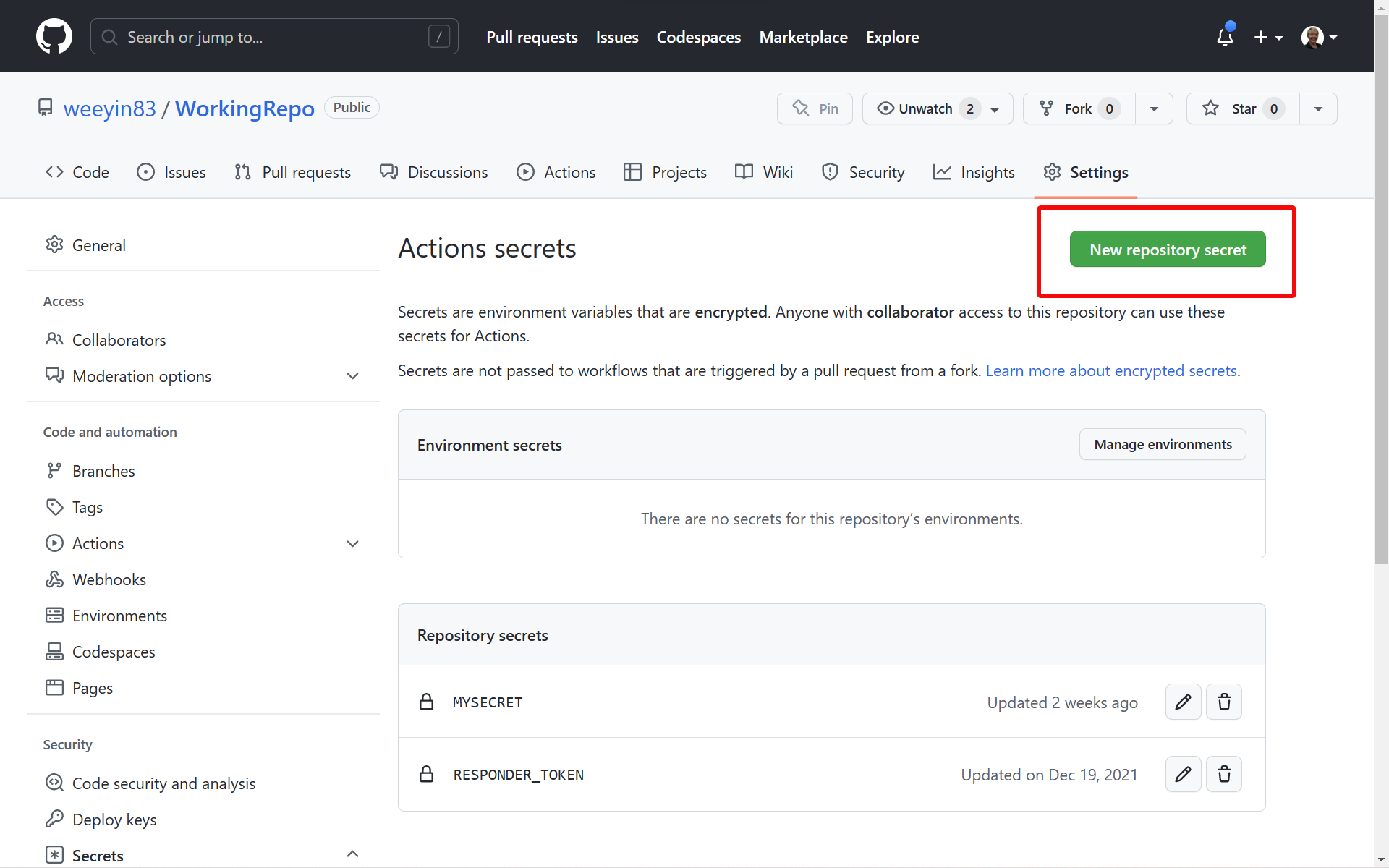
Click on New Repository Secret.
Complete the following fields:
- Name, give the secret a suitable name, and don’t use any space or special characters. Underscores are usable.
- Value, enter the secrets.
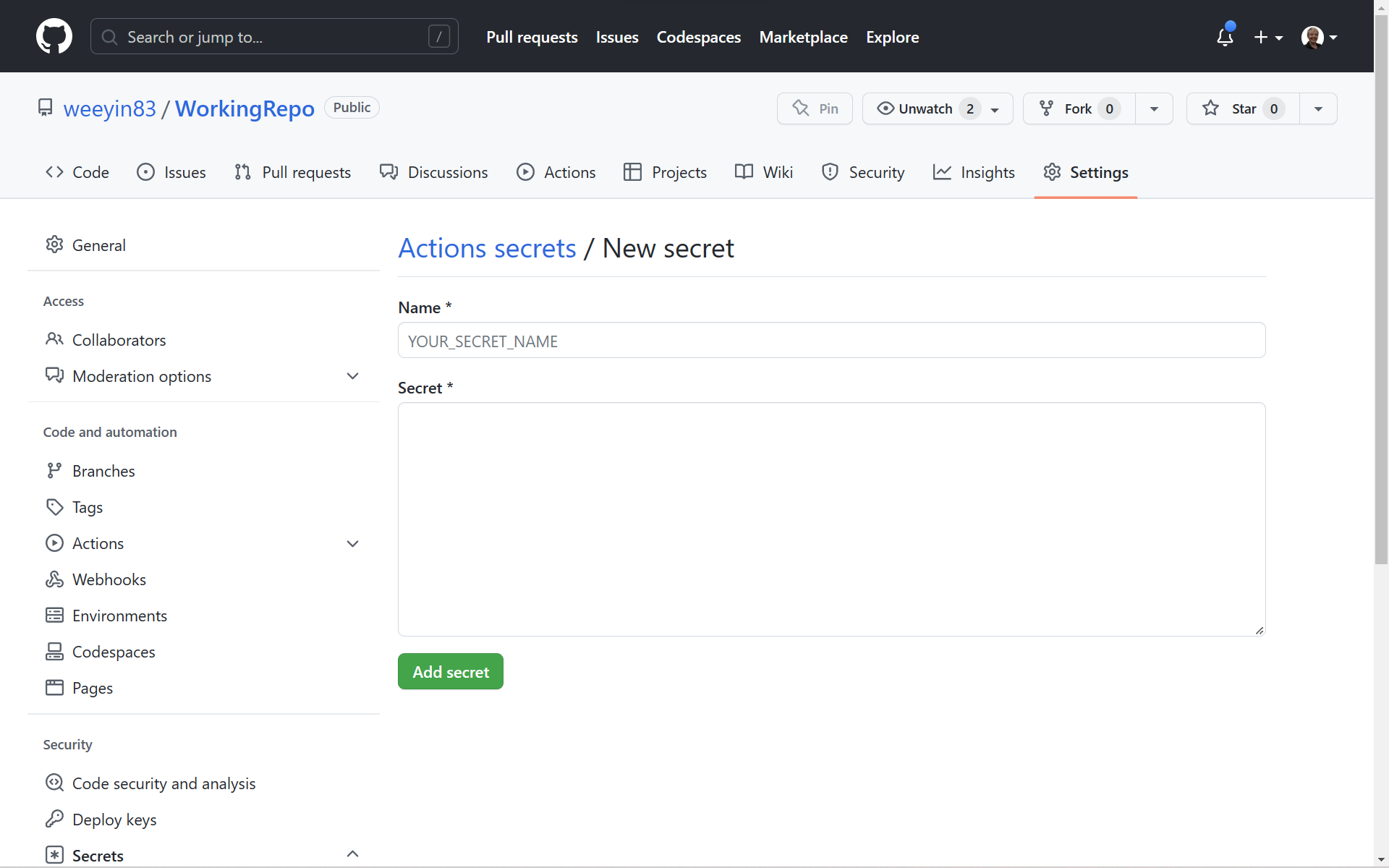
Click on Add Secret.
You are able to update this secret whenever you need to change it.
Environment secrets
Within GitHub, you can specify different environments in which to target for your deployments, such as production, staging, or development.
If you have a public or an enterprise licence you can set environment-specific secrets that will only work for that environment.
There is a limit of secrets per environment, 100.
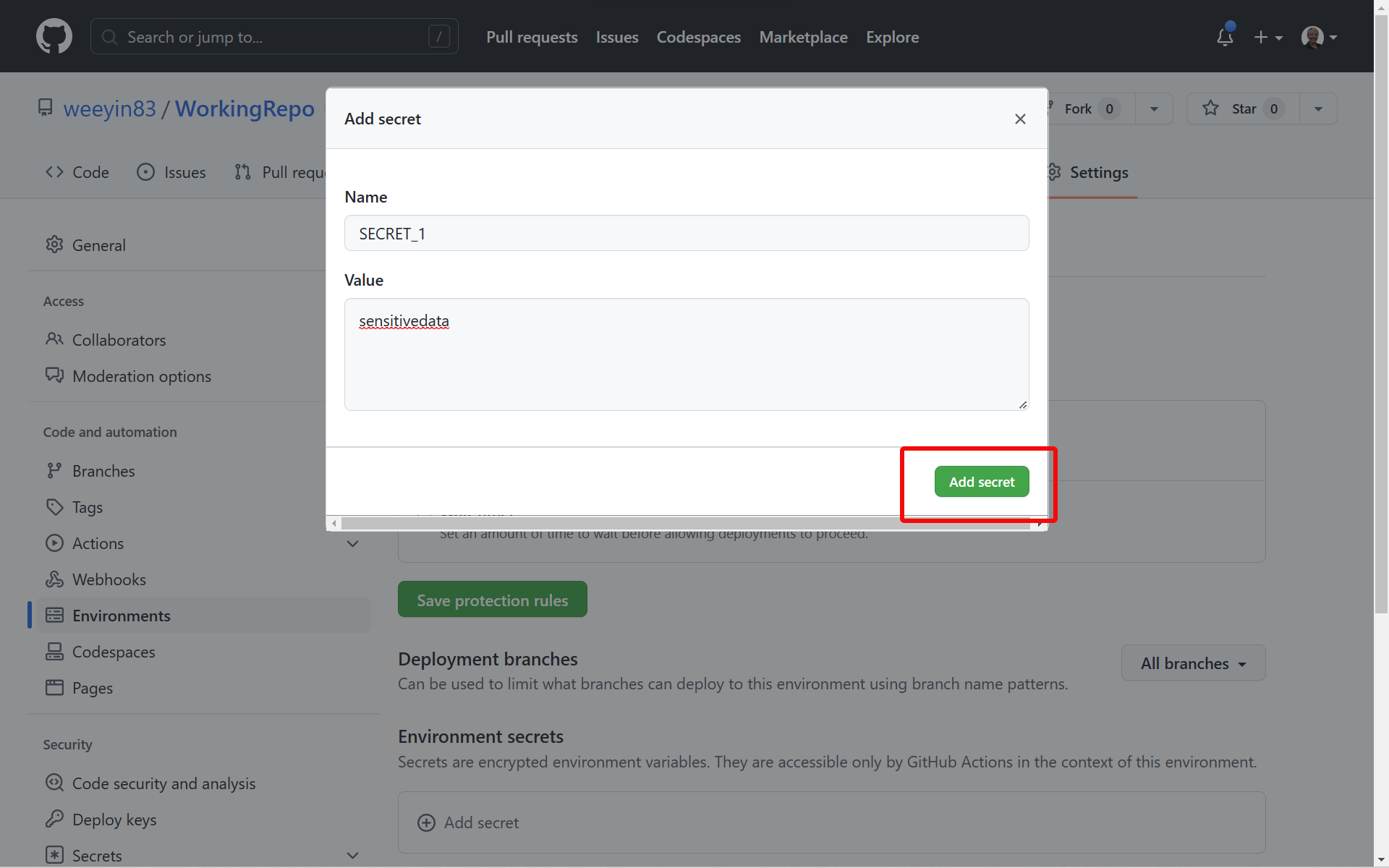
Add an environment secret when creating a new environment
Open your project’s repository and click on Settings in the top menu
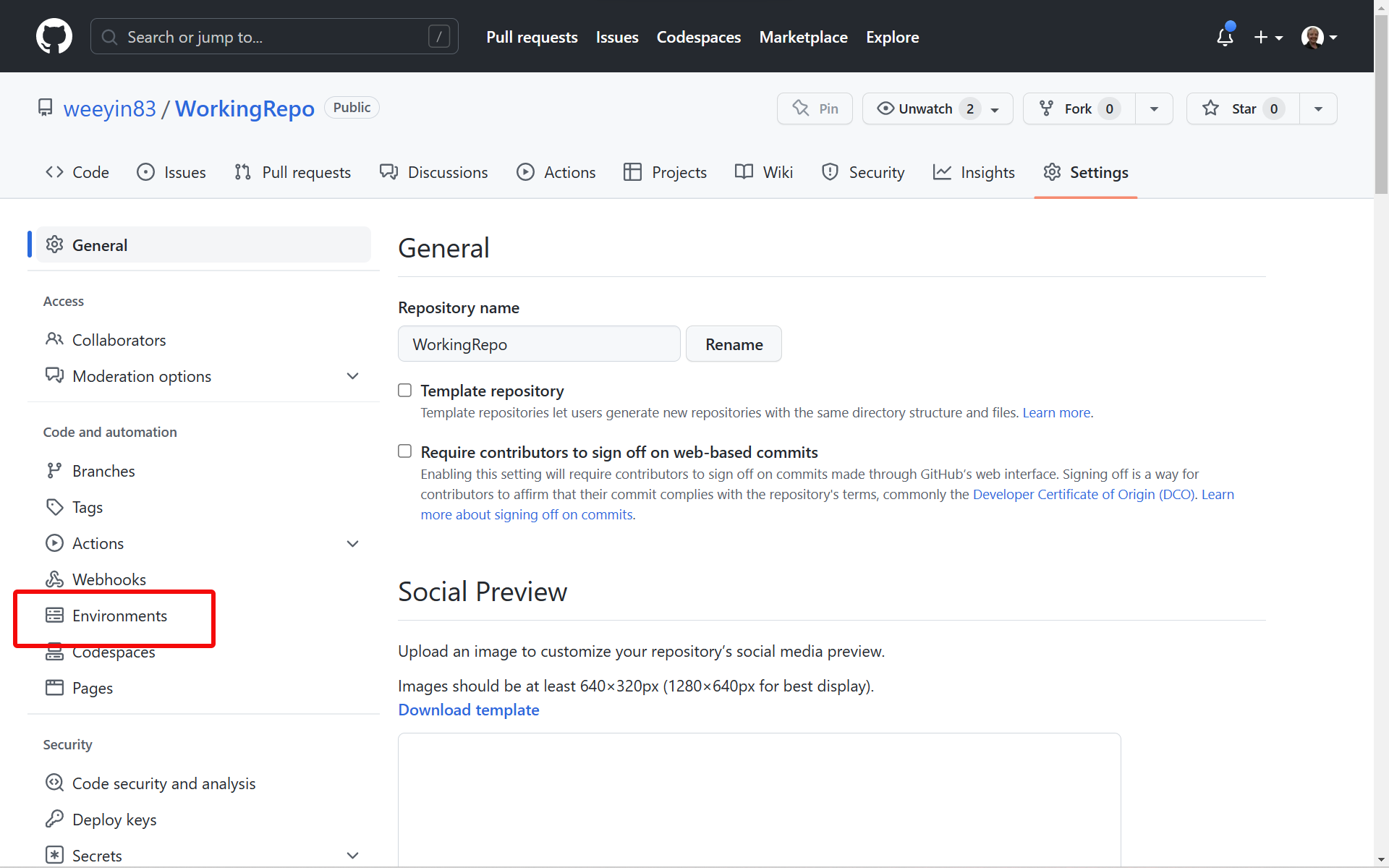
Click Environments in the left hand side menu.
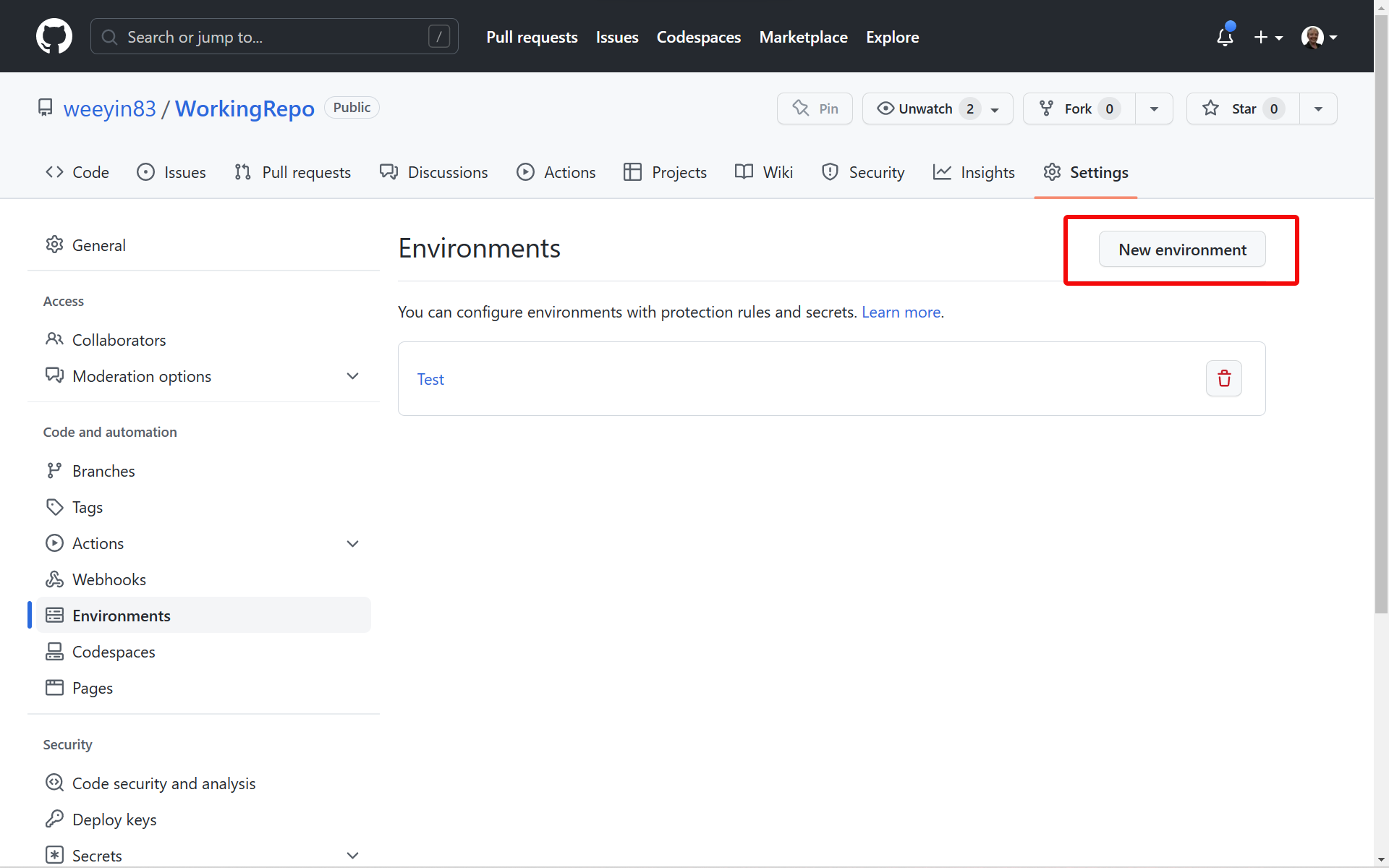
Click on New environment.
Enter a name for your environment and click Configure environment.
Configure the environment’s protection rules and deployment branches as you require them and then click on Add Secret.
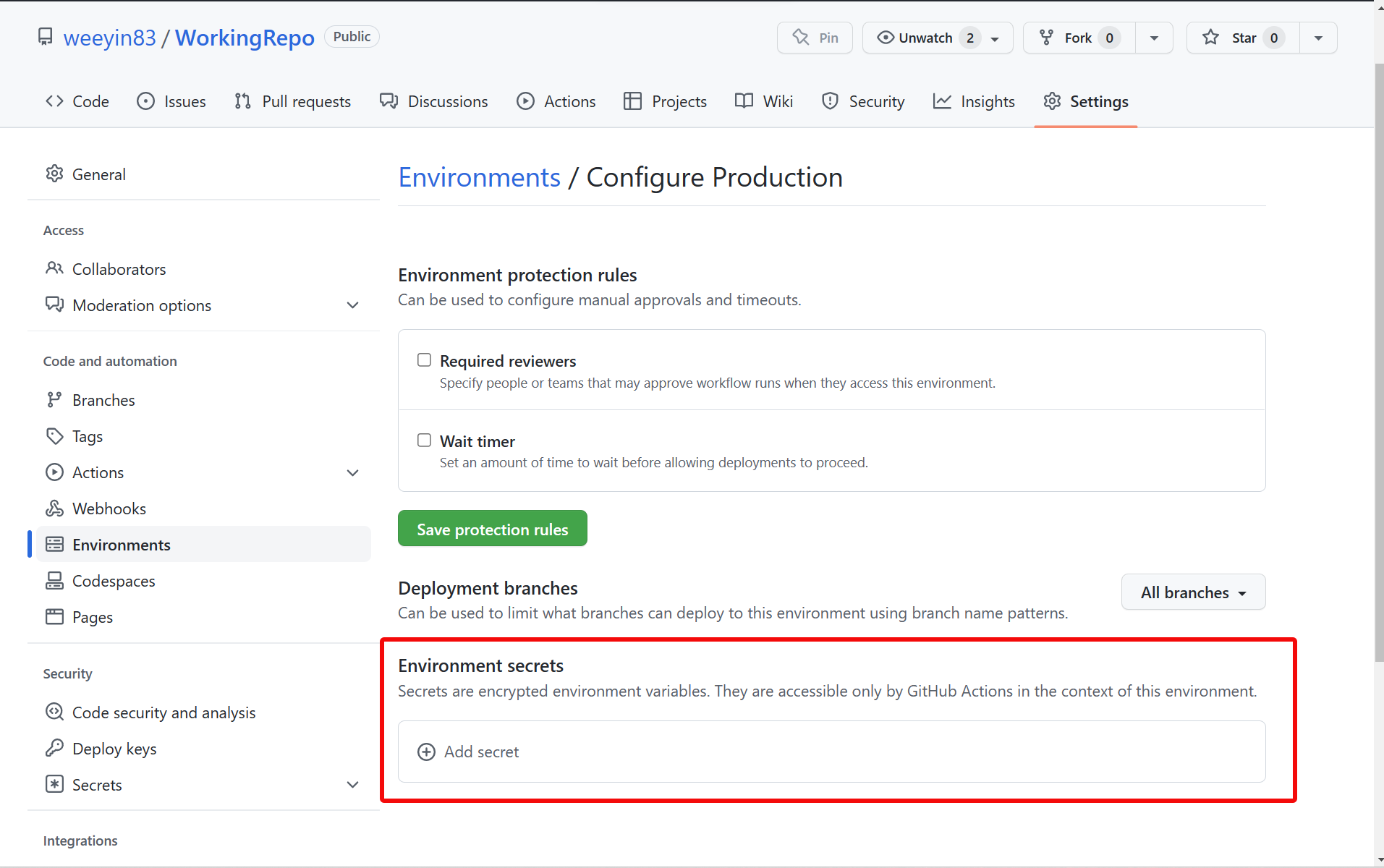
Complete the following fields:
- Name, give the secret a suitable name, don’t use any space or special characters. Underscores are usable.
- Value, enter the secrets.
Click on Add Secret.
If you wish to change the secret or add others for that environment in the future you can do so through Settings > Secrets > Actions.
Organization secrets
An organization within GitHub is a shared account for businesses or open-source projects to collaborate across many projects.
In 2020 GitHub announced organization secrets. A way of sharing secrets across repositories.
There are access policies available which allow you to control which repositories have access to an organization secret.
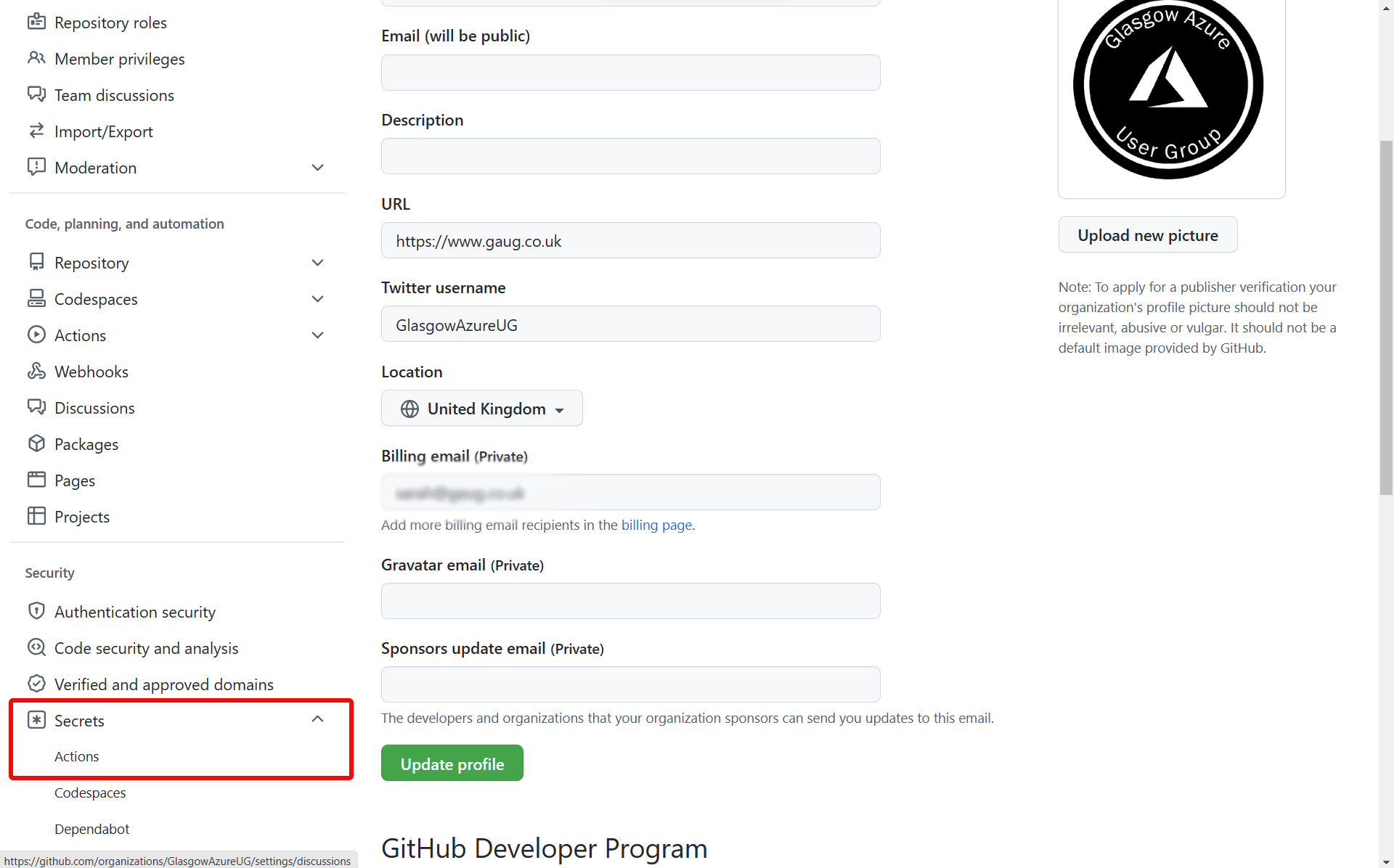
Add an organization secret
Open your organization’s page in GitHub and click Settings in the top menu.
Click Secrets in the left menu.
Click on Actions.
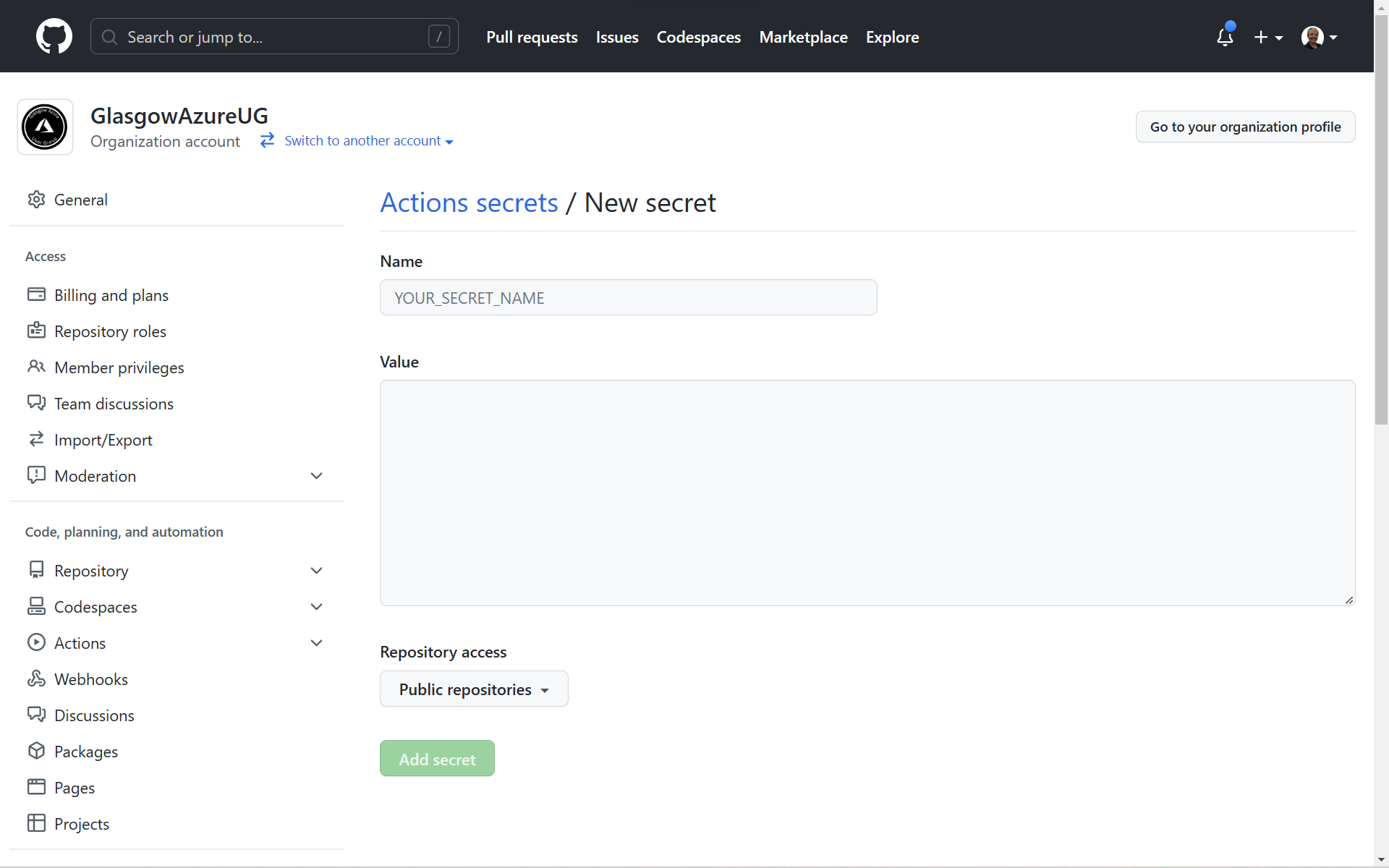
Now select New organization secret.
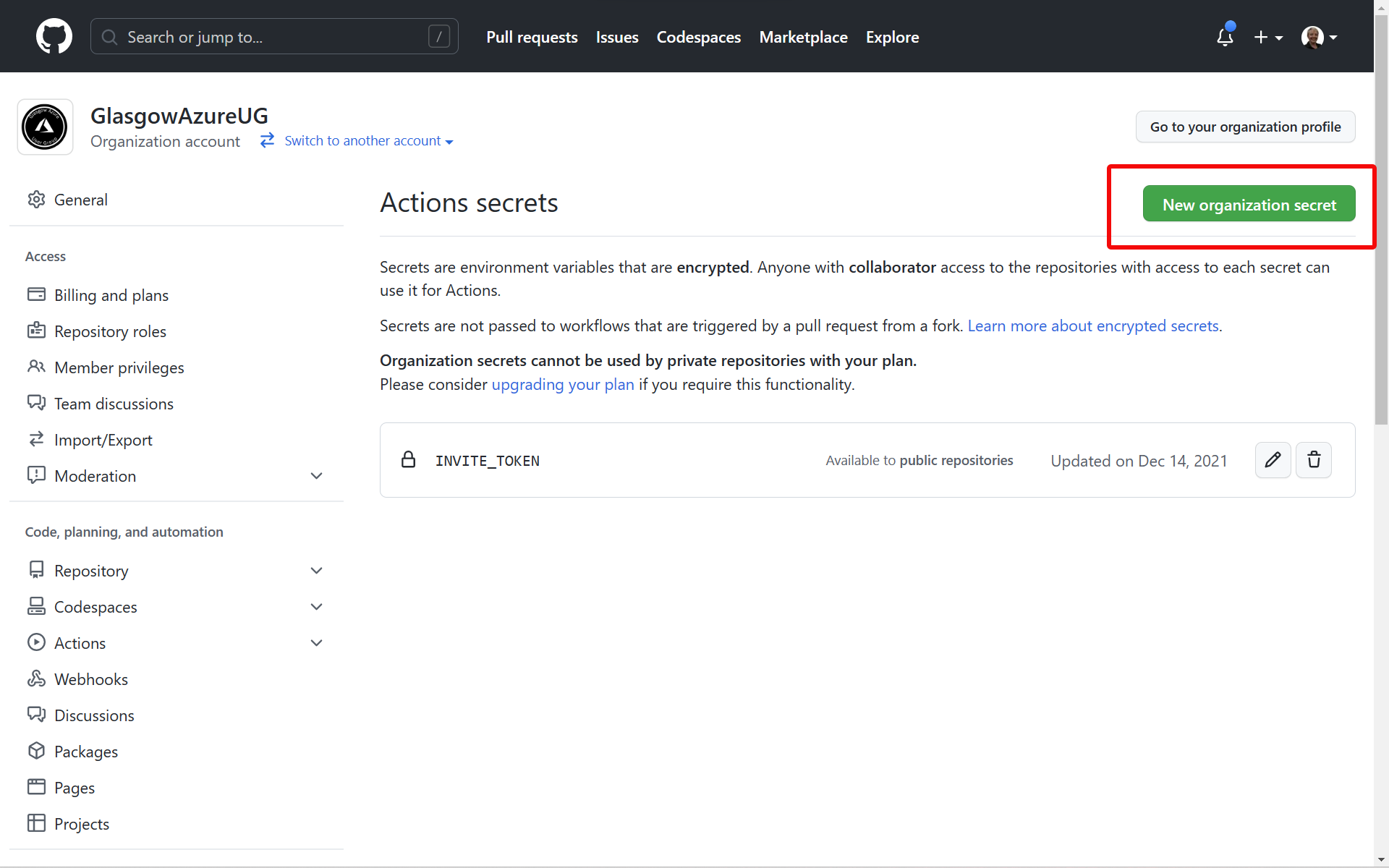
Complete the following fields:
- Name, give the secret a suitable name, don’t use any space or special characters. Underscores are usable.
- Value, enter the secrets.
- Repository access, select the relevant policy or repositories you wish to be able to see this secret.
Click on Add Secret.
Using secrets in GitHub Actions workflows
Within GitHub Actions workflows contexts are how GitHub pulls information from various sources. We can use the context of the secret to call your secret data in workflows.
As an example, if you are trying to interact with Azure during a workflow. Perhaps you are deploying an Azure Bicep template. You need to provide GitHub with credentials to your Azure environment.
You might add a step such as:
- name: Azure Login
uses: Azure/login@v1.4.3
with:
creds: ${{ secrets.AZURE_CREDENTIALS }}
Here we are using the GitHub Actions action “Azure Login”. Our Azure credentials are stored within a repository secret and we are calling them into the workflow without exposing the information to the public.
GitHub Actions Secrets - Security Best Practices
If you’d like to learn more about GitHub Actions please do check out my other blog posts.
